Comprehensive Approach to Risk Mitigation
A unified security strategy across application, middleware, databases, and operating systems will help prevent and combat potential threats from bad actors. Our expert staff will partner with your team through our proven defense-in-depth process to provide vital advisement and recommendations on hardening and compliance measures across your system’s infrastructure.
- Discover & Harden
- Incident Response
- Threat Intelligence
-
Security Assessments
We identify weaknesses and opportunities to improve the security of your systems by providing guidance on hardening techniques and configuration adjustments
-
Audit Compliance
We work with your audit teams to help you adjust your controls to stay compliant under a third-party support model
-
On-Demand Vulnerability Management
Our security staff is standing by to resolve your vulnerability concerns, even your customizations
-
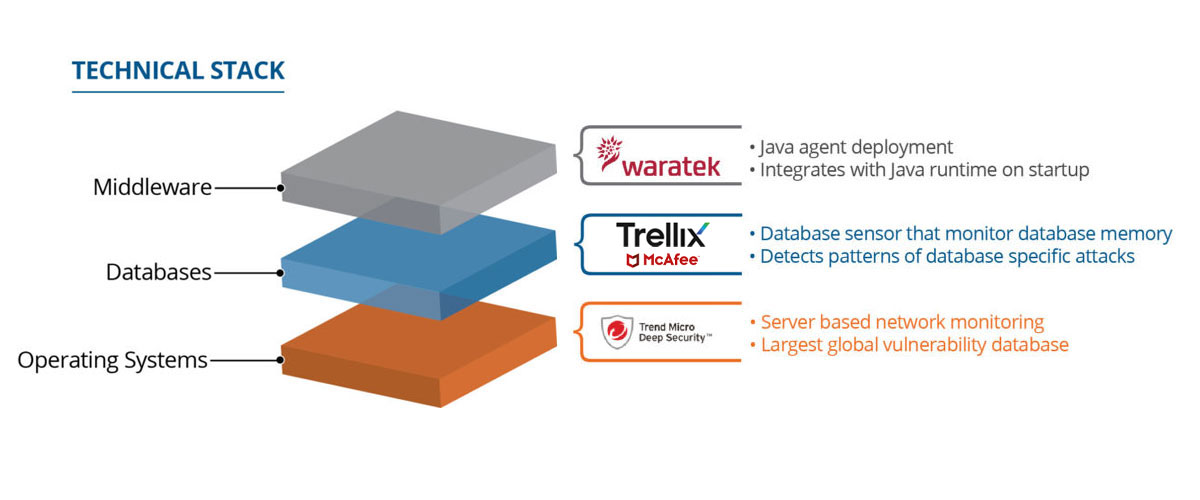
Security Tooling
In addition, we offer a suite of security products to complement your existing security to allow it to adjust to a third-party support model
-
Security Bulletins
We continually evaluate OEM security issues and publish regular bulletins describing product vulnerabilities and best practices for improving hardening standards and mitigating these vulnerabilities.
Vendor Patching | Vulnerability Management | |
|---|---|---|
| TIMING | Patches are not timely (can take months or even years to receive final fix). | Compensating controls and configuration suggestions are relayed to the customer within days to weeks. |
| SPECIFICITY | Patches are one-size-fits-all and may be problematic for customizations. | Receive fixes tailored to your system. |
| VERSIONS | Patches may not be available for older versions and applications. | By addressing issues at the infrastructure level, you protect the entire stack, regardless of app versions. |
| TESTING | Patches require valuable time to test and install. | Isolate testing to the area effected by the vulnerability rather than the entire system. |
| APPLICATION | Often organizations are too short staffed or don’t have a patch management system in place to regularly apply patches. | Address the issue at the source and convey the proper hardening techniques. |